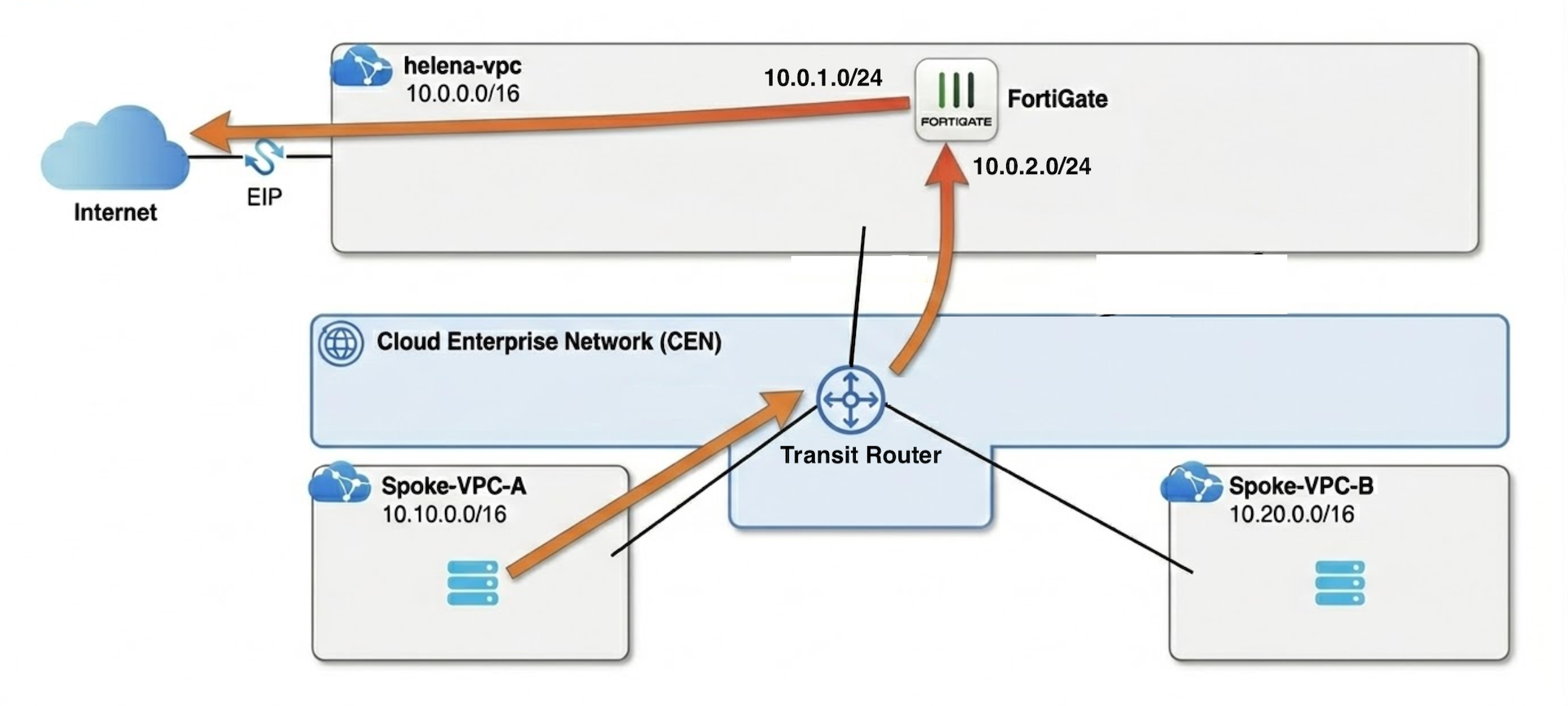
Cloud Enterprise Network (CEN) is a high-performance networking service that provides scale-out connectivity to Alibaba Cloud’s global backbone. At the heart of this architecture is the Transit Router (TR), an Enterprise-grade managed hub that acts as the intelligent transit point for all connected VPC spokes and security services.
In this lab, we leverage this hub-and-spoke relationship to build a centralized security architecture. By connecting multiple application VPCs to the Transit Router, we transform our FortiGate VM into a centralized Egress Firewall.
VPC
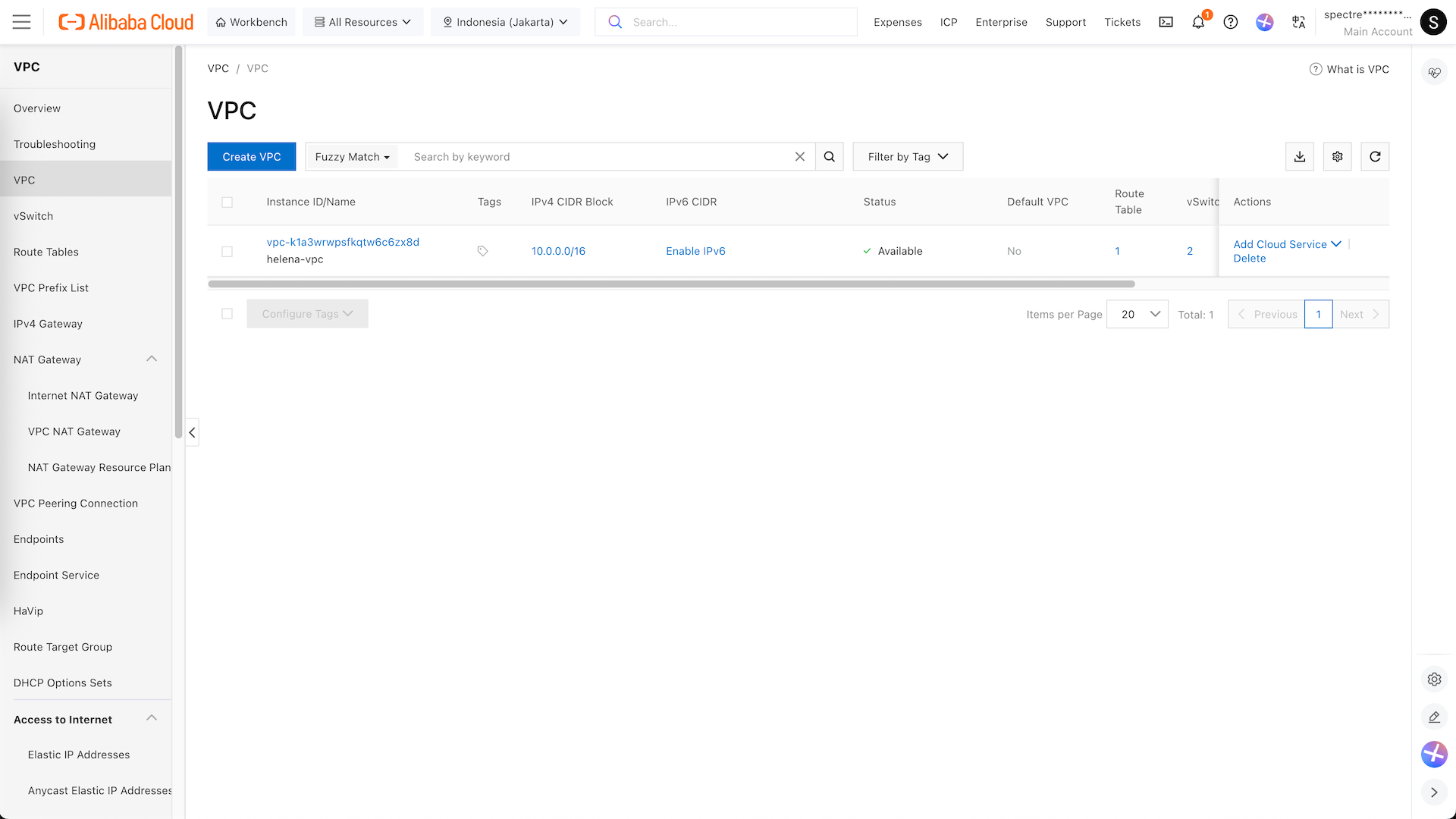
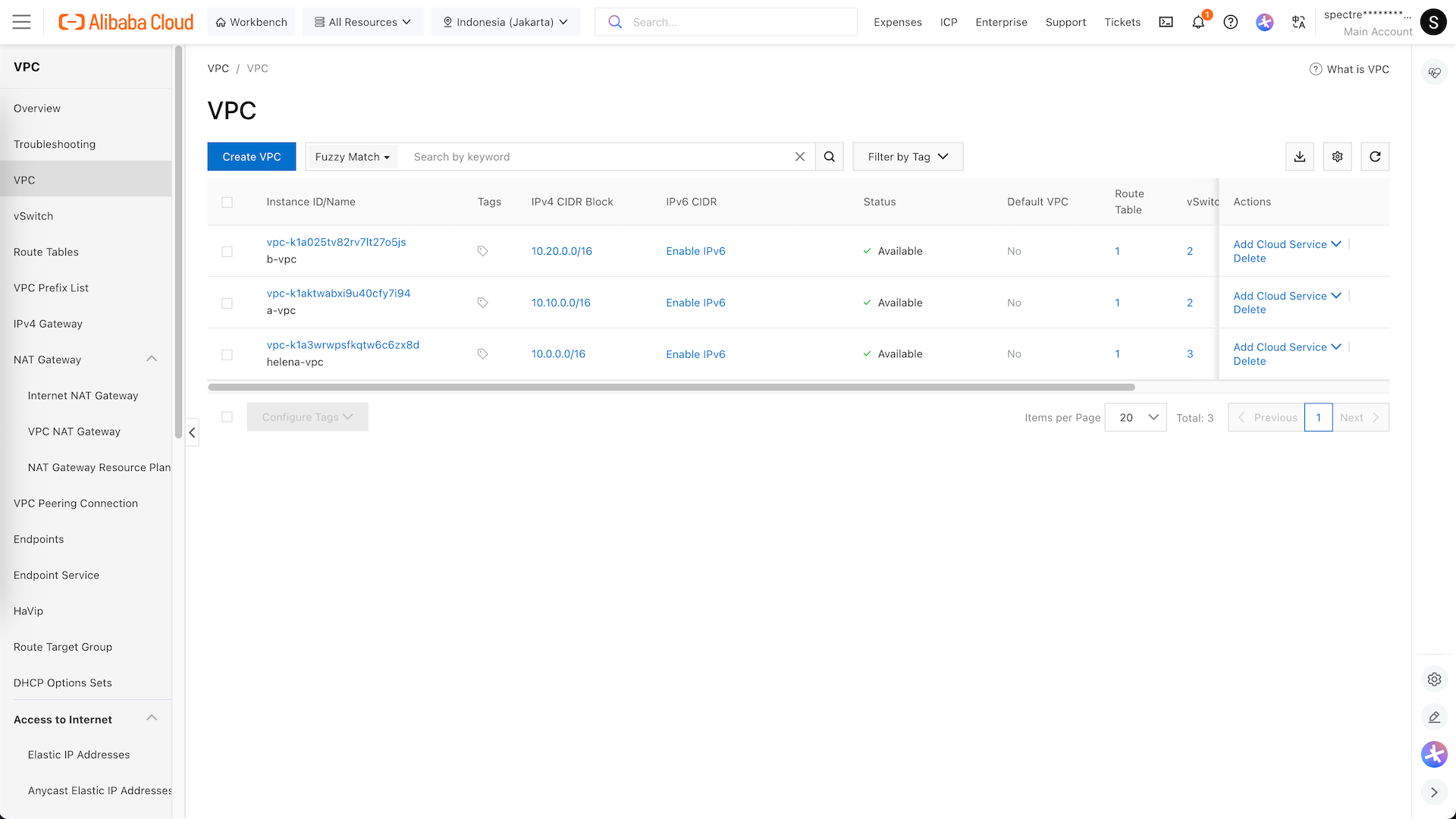
Here we are continuing from this Albaba Cloud Setup lab, where we already have Fortigate and VPC Helena configured
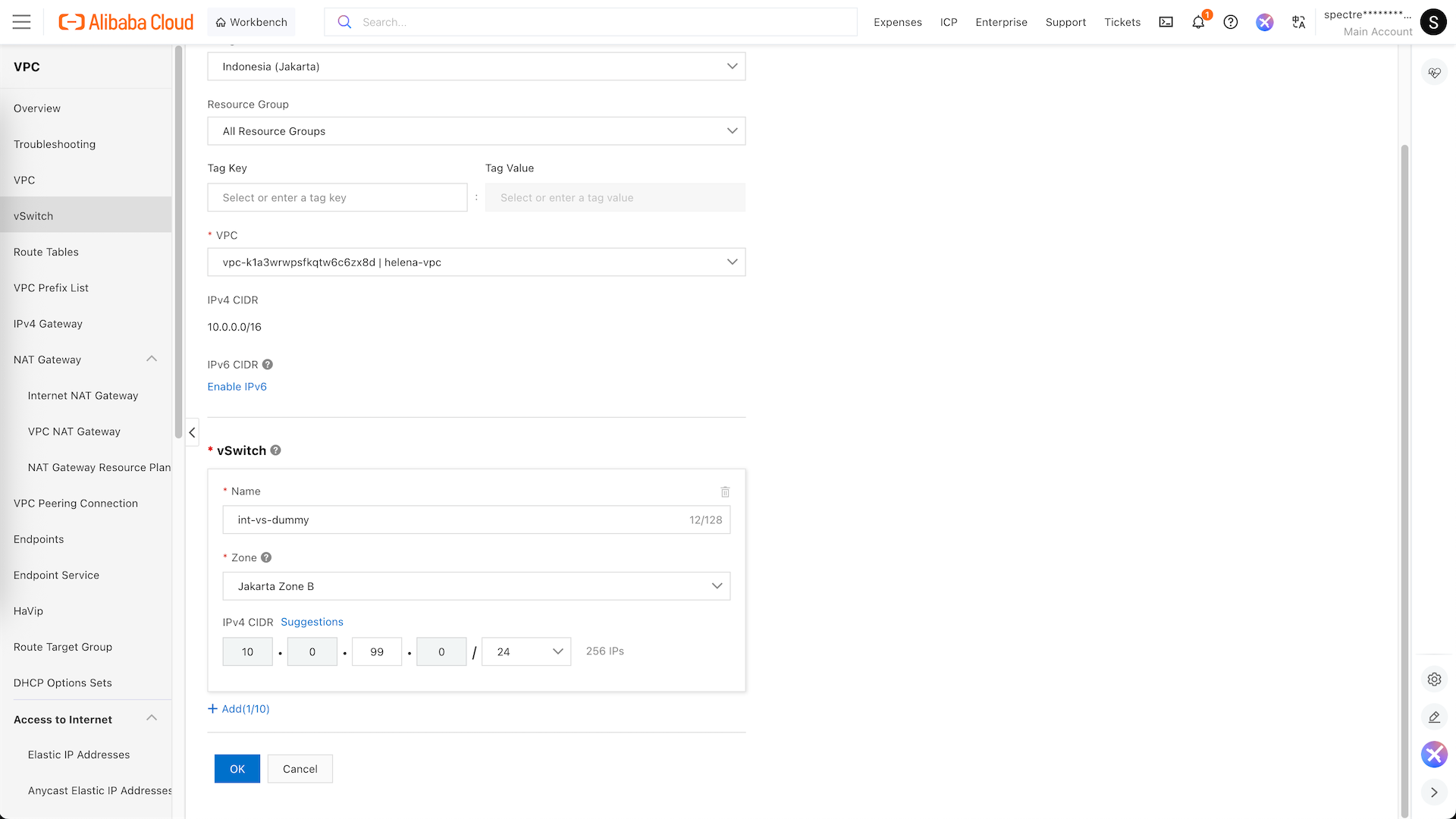
CEN requires us to have multi-zone redundnacy network, so for our helena-vpc we will create additional dummy vs on different zone to satisfy this requirement
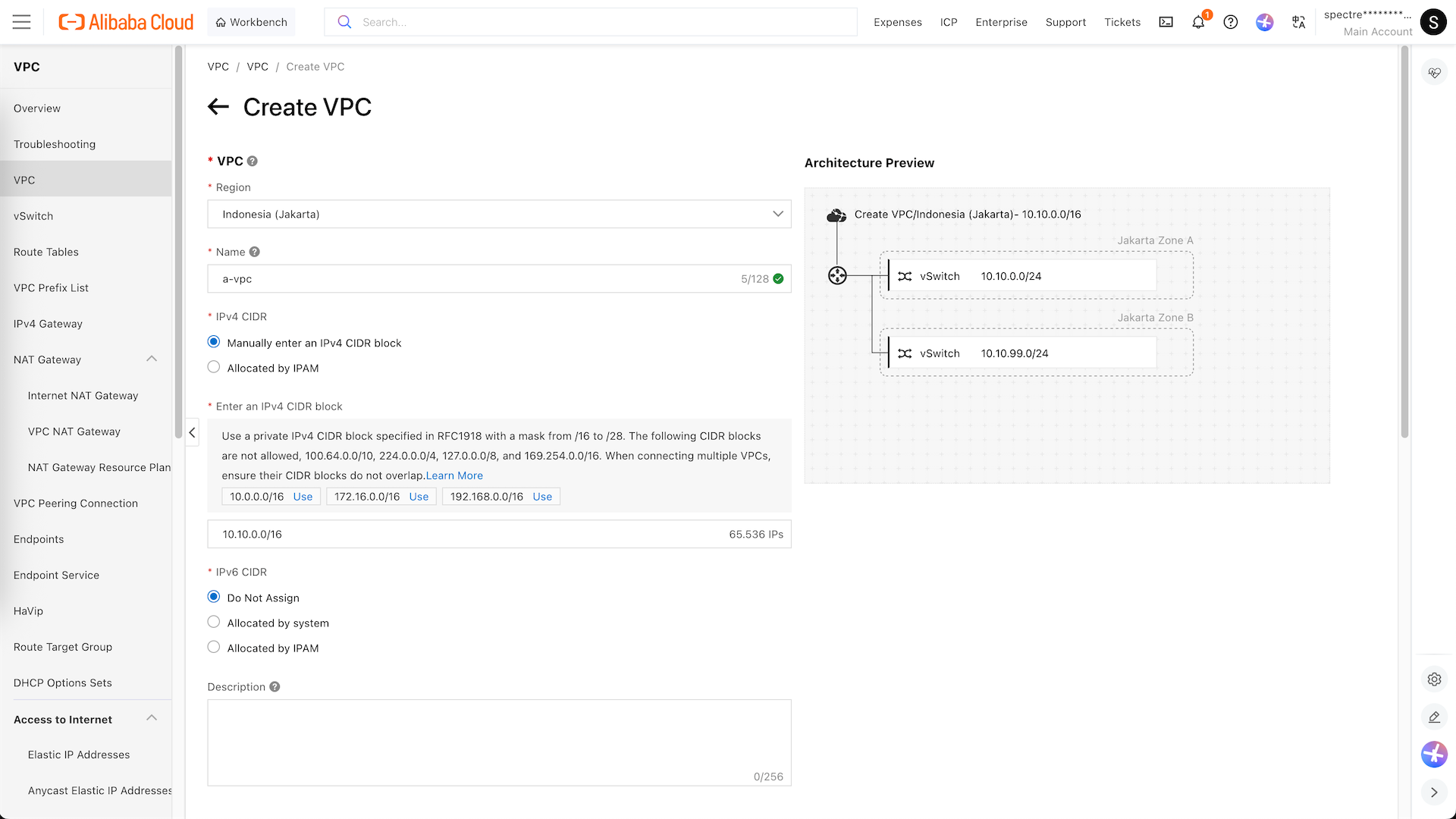
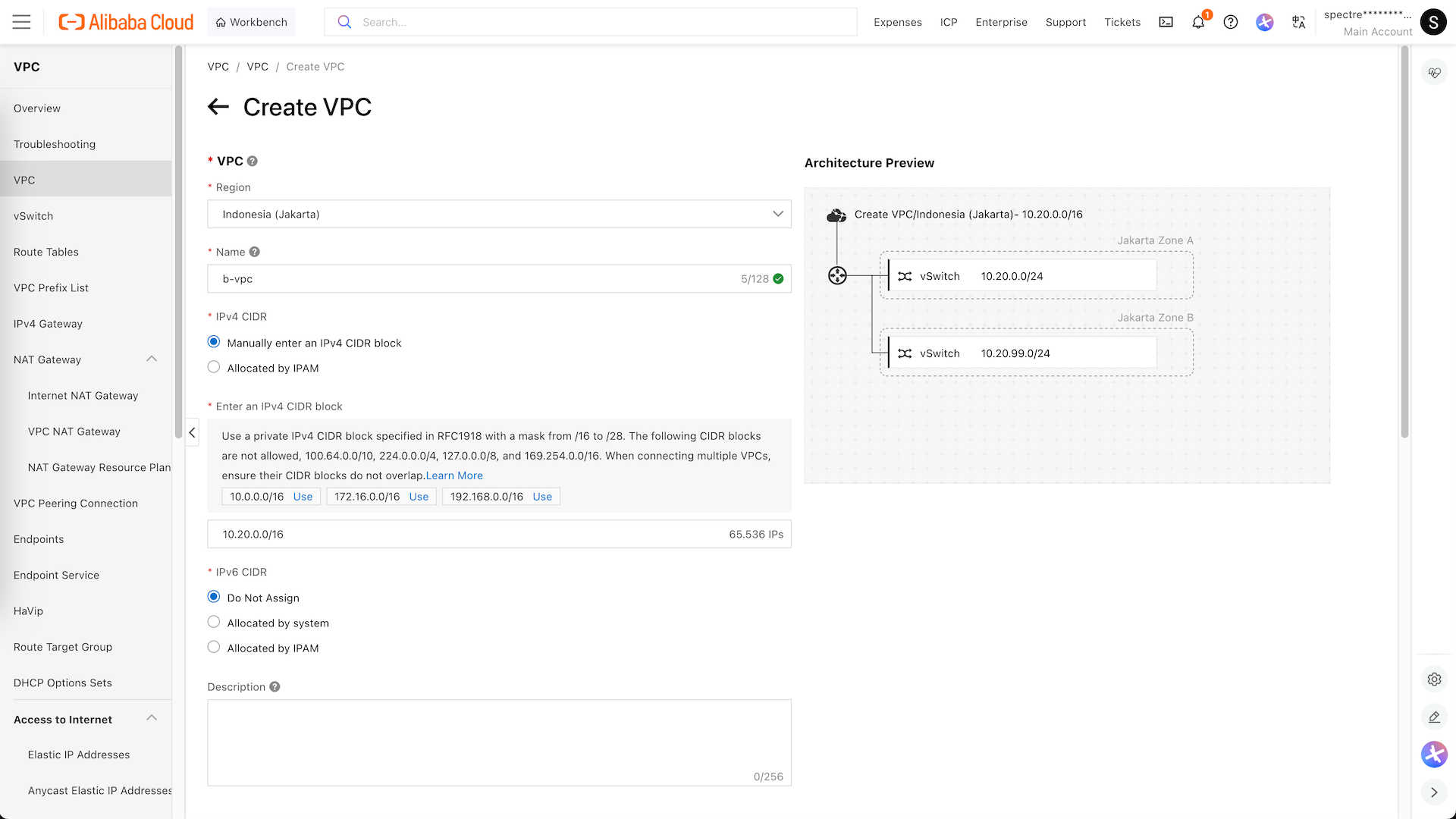
Next we create the spokes VPC, starting with a-vpc on 10.10.0.0/24 along with its dummy vs
Same goes for vpc-b on 10.20.0.0/24
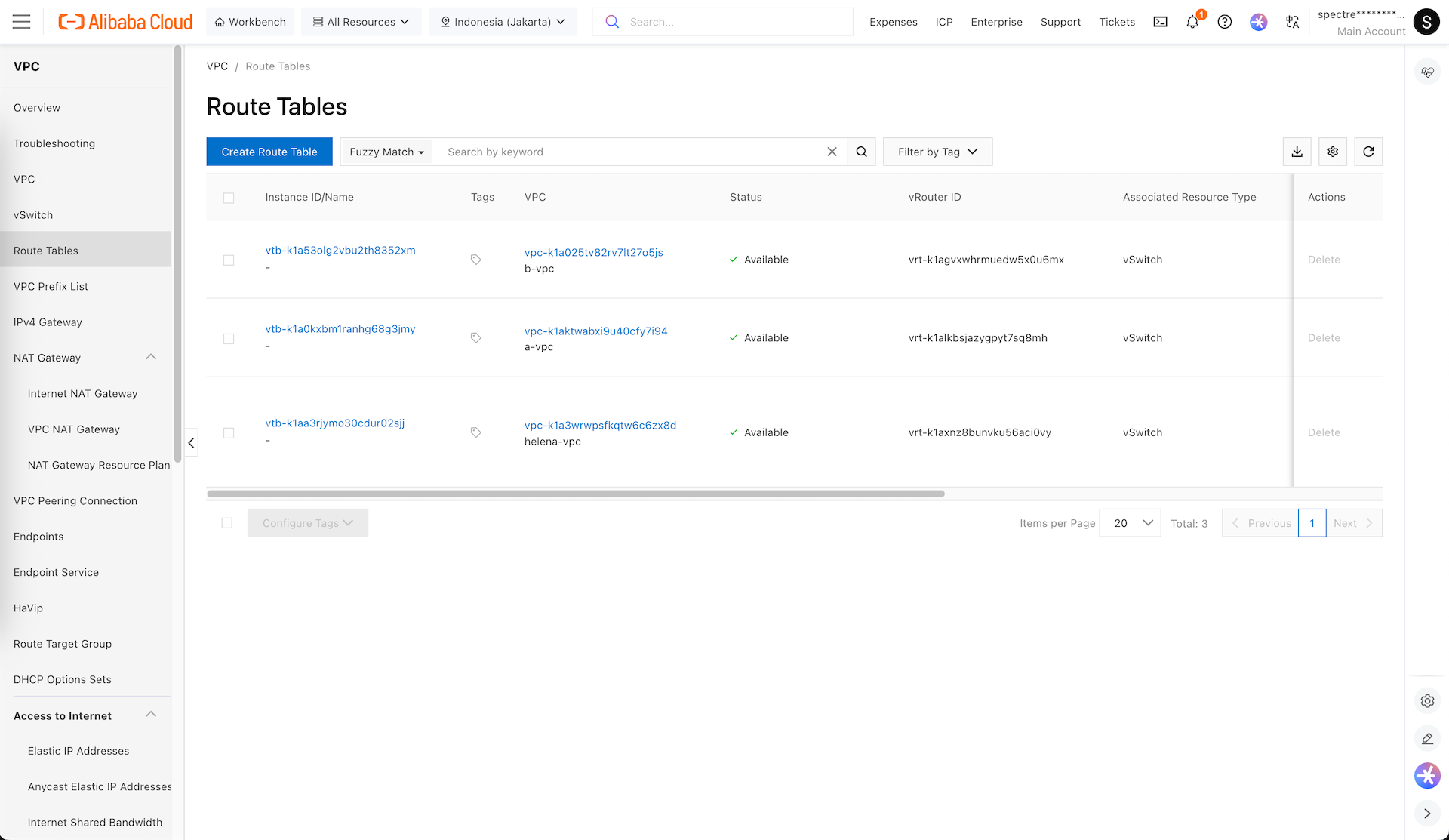
And here we have our 3 VPCs
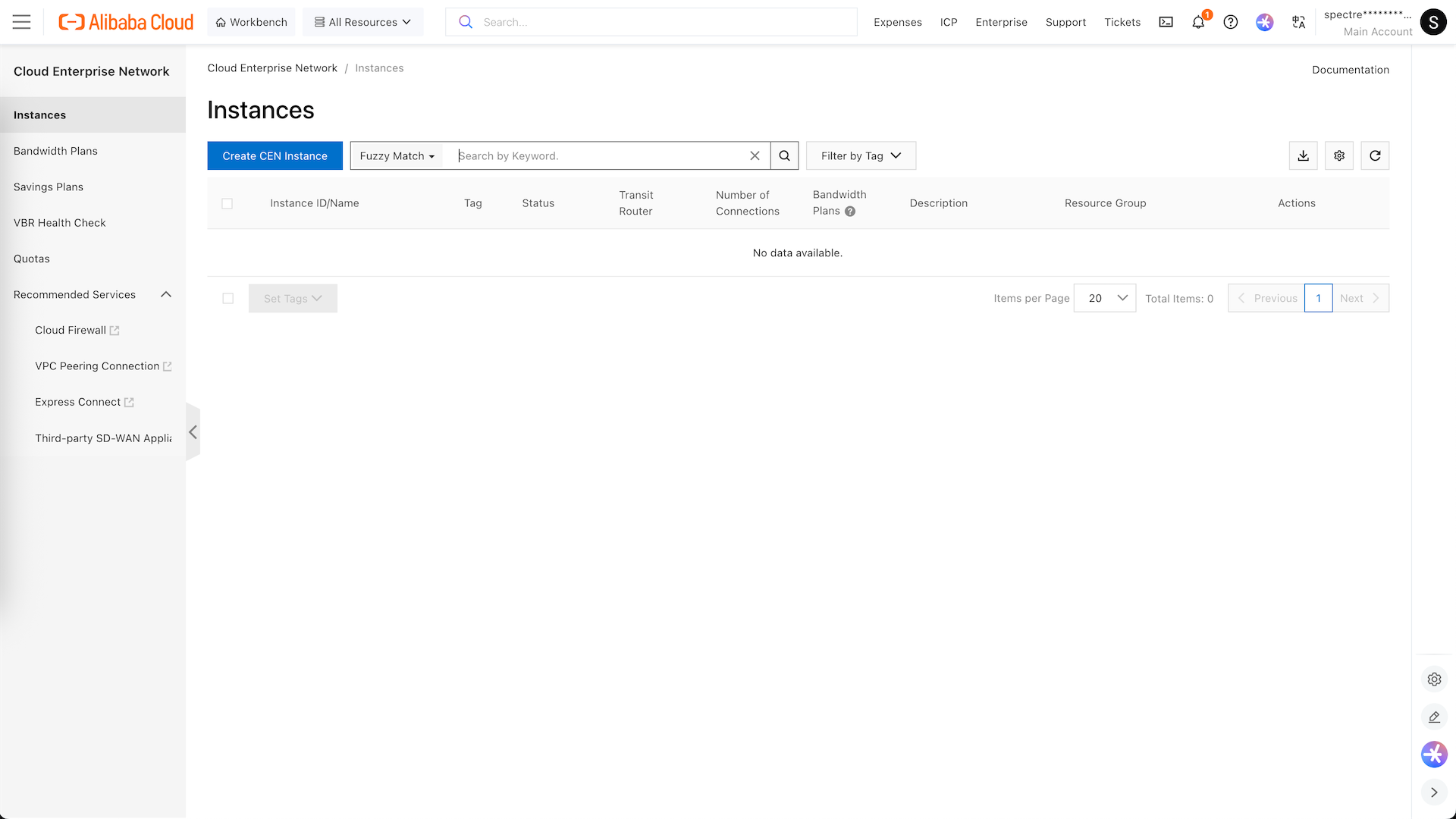
CEN
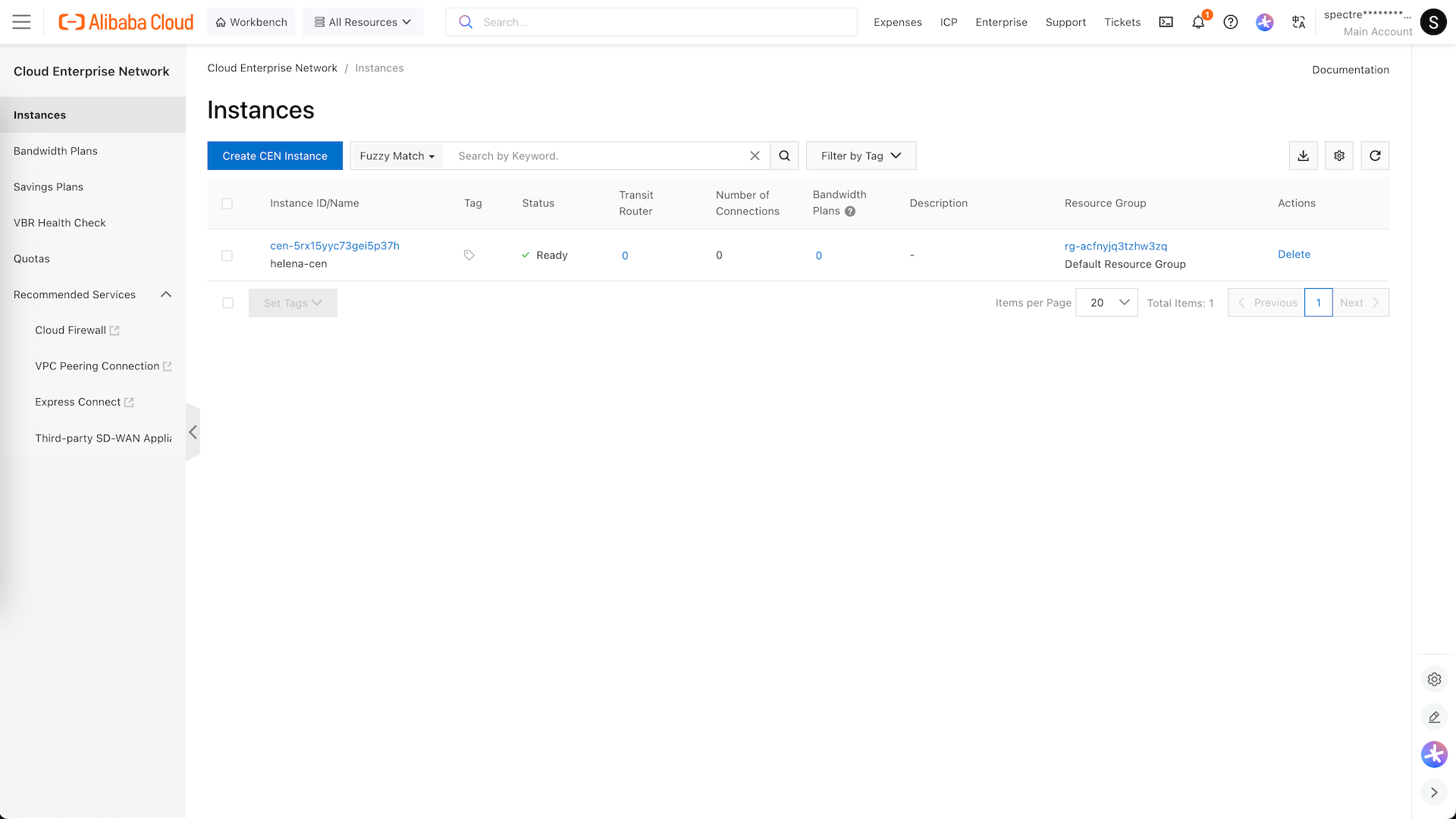
Next we configure the Cloud Enterprise Network Instance
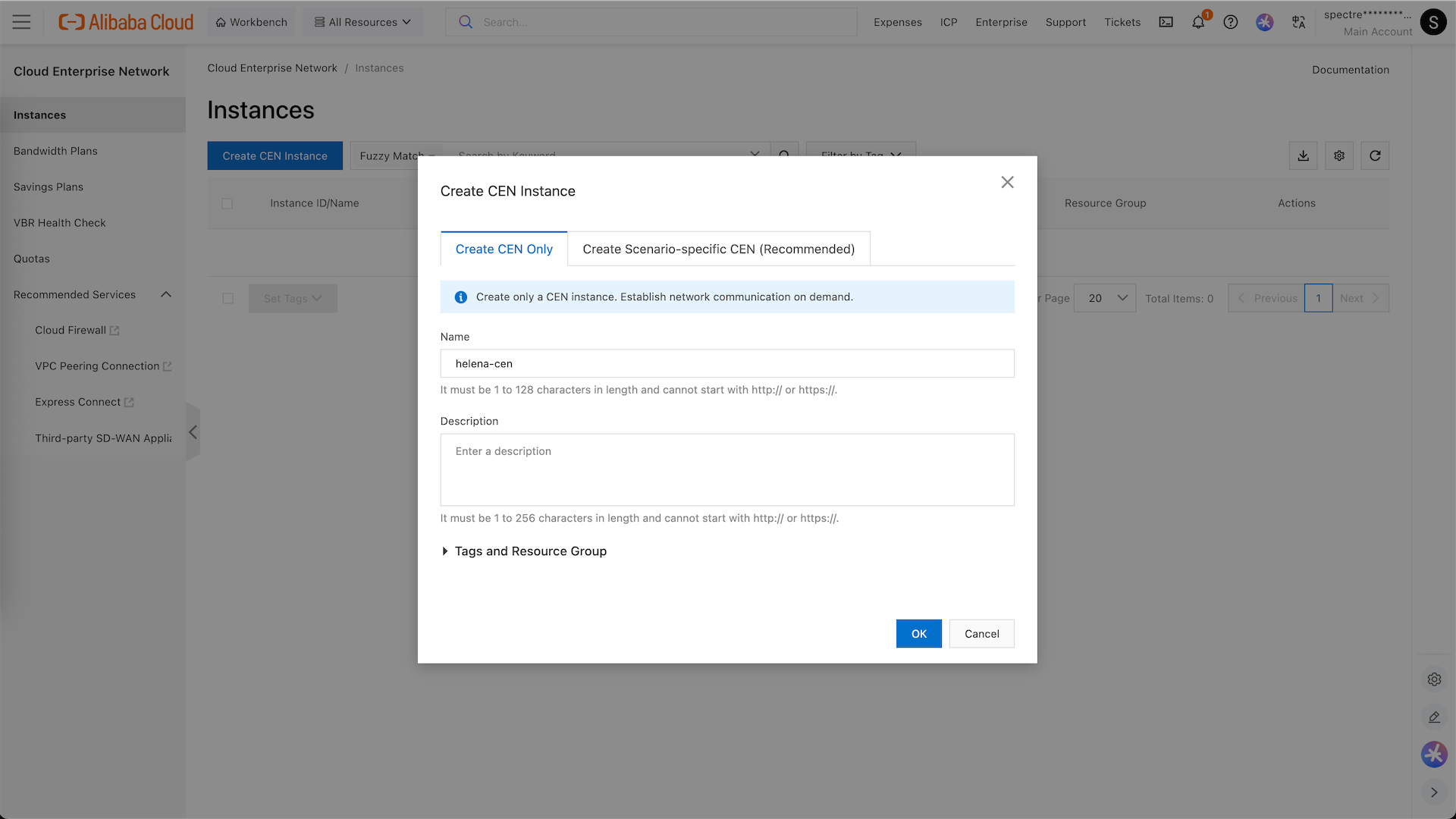
Here we create the CEN instance named helena-cen
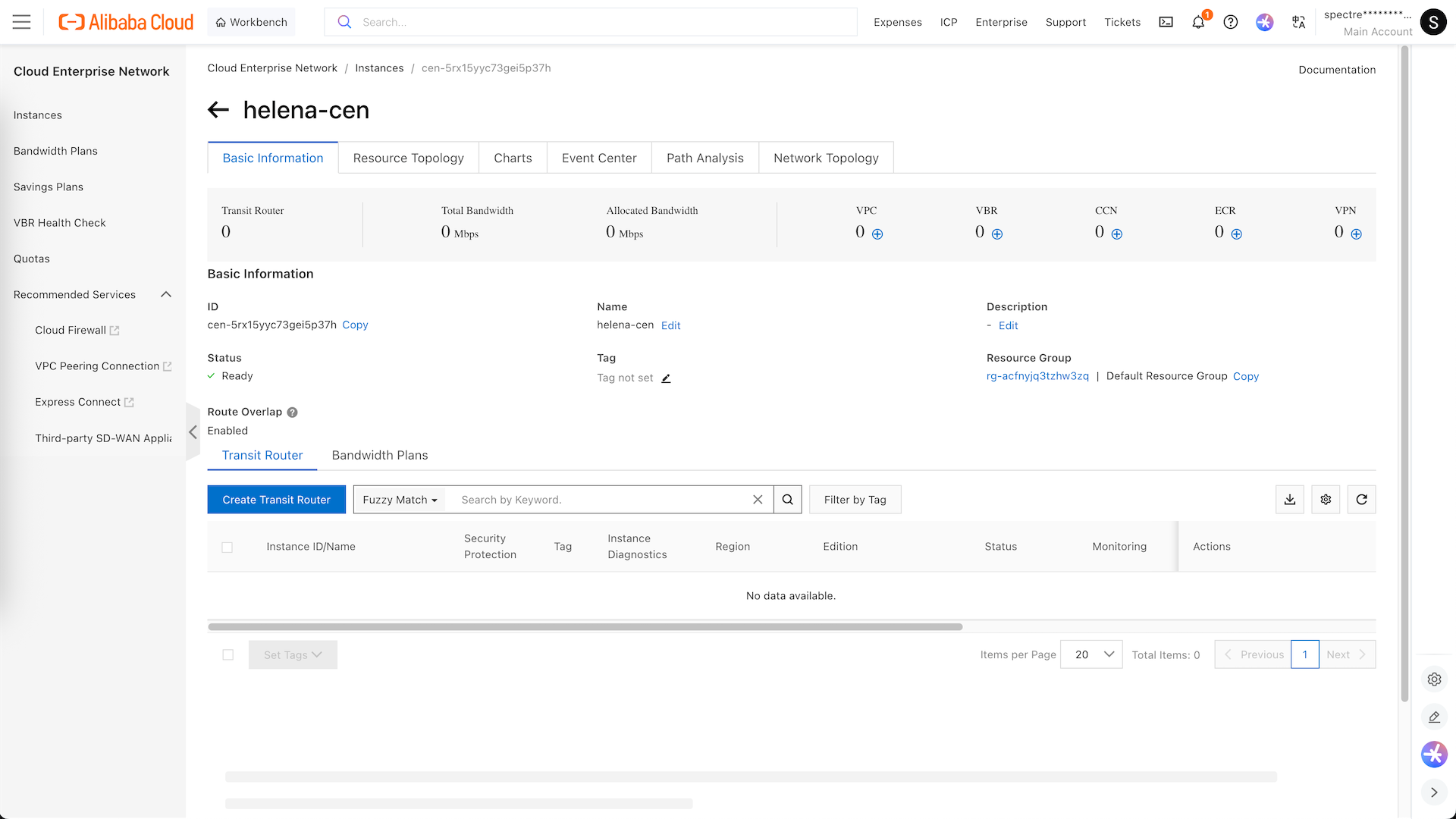
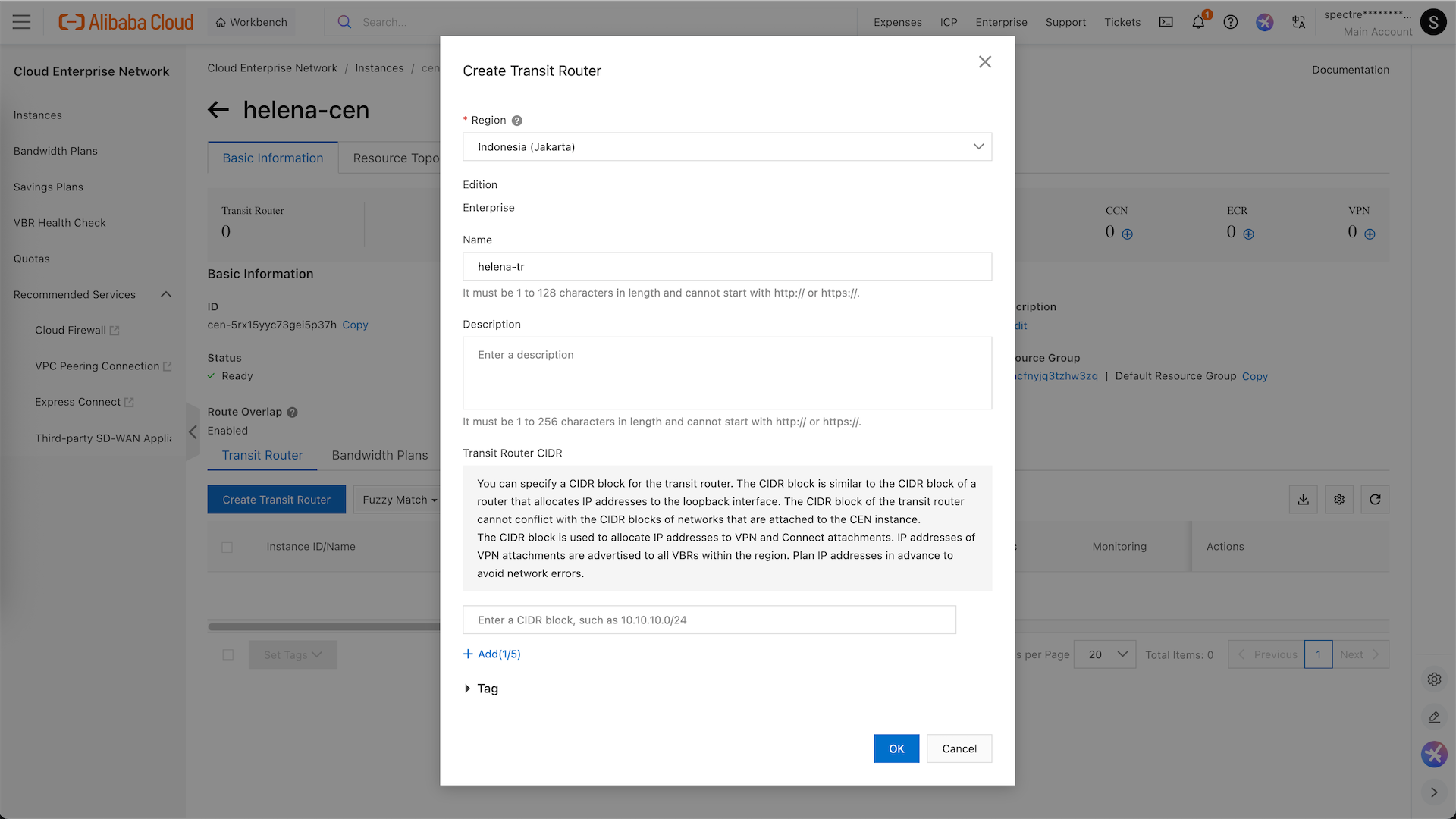
Open the helena-cen instance and create a Transit Router
We name it helena-tr
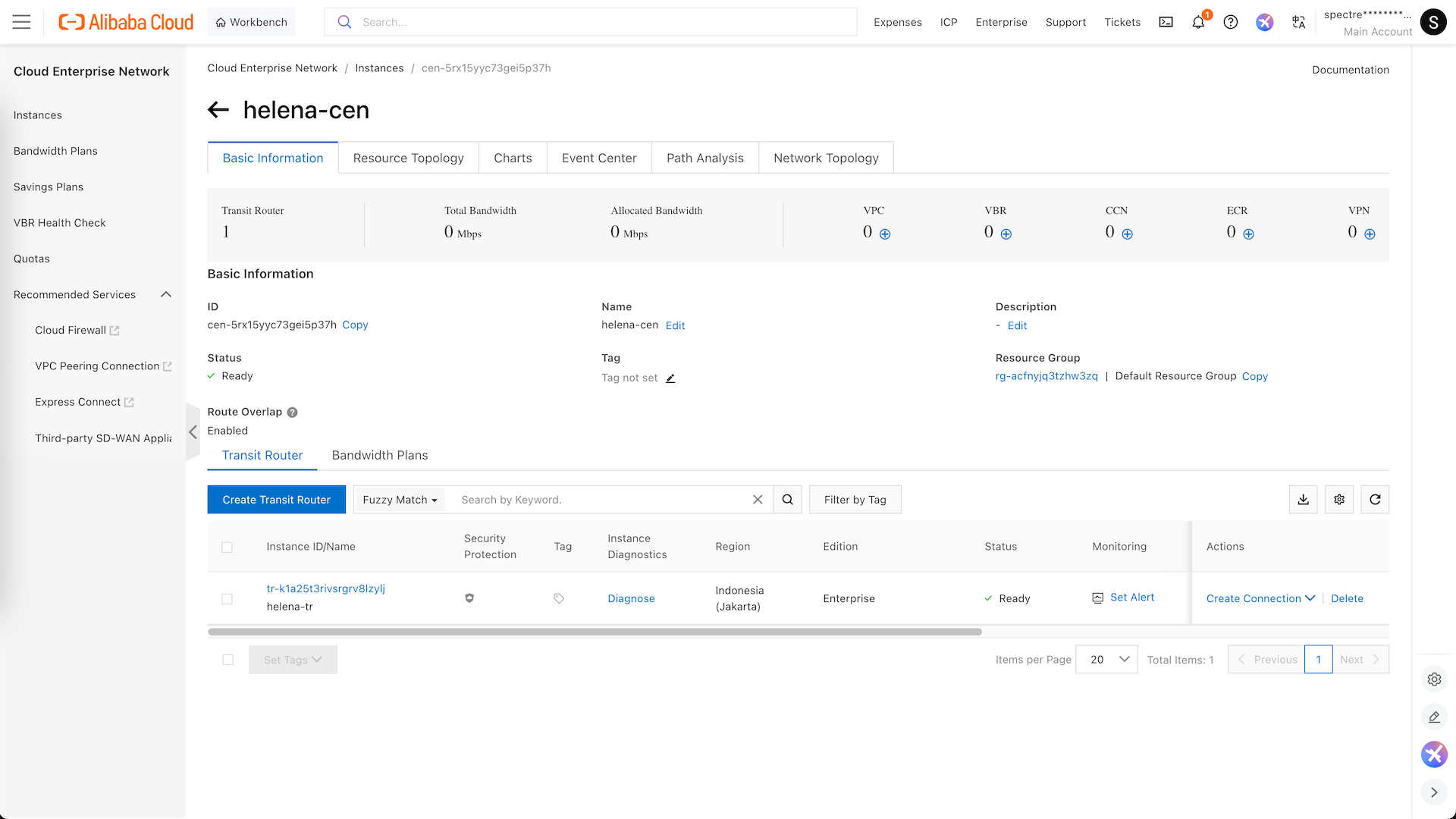
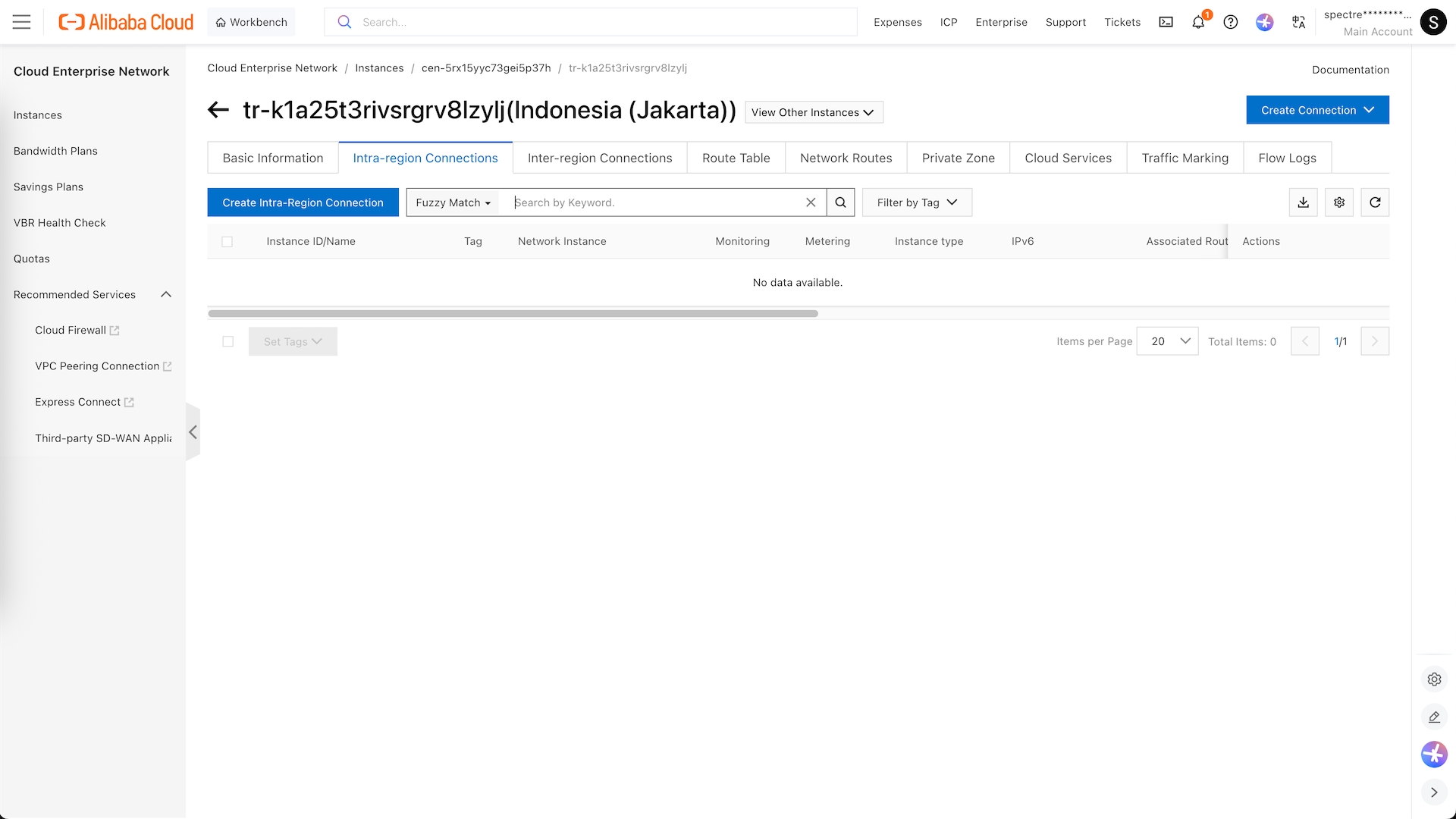
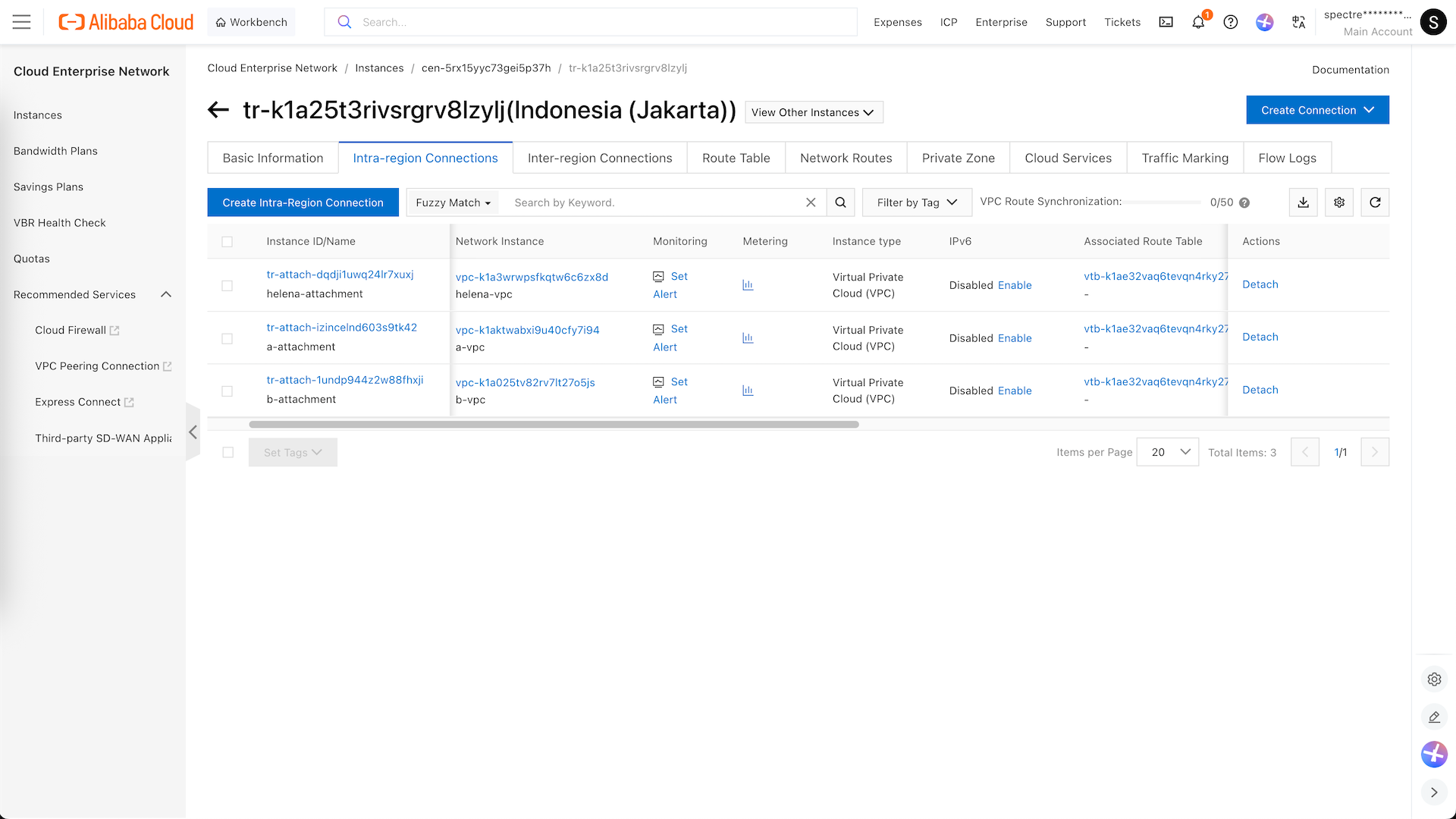
Open the Transit Router and here we will create the Intra-region connections to our 3 VPCs
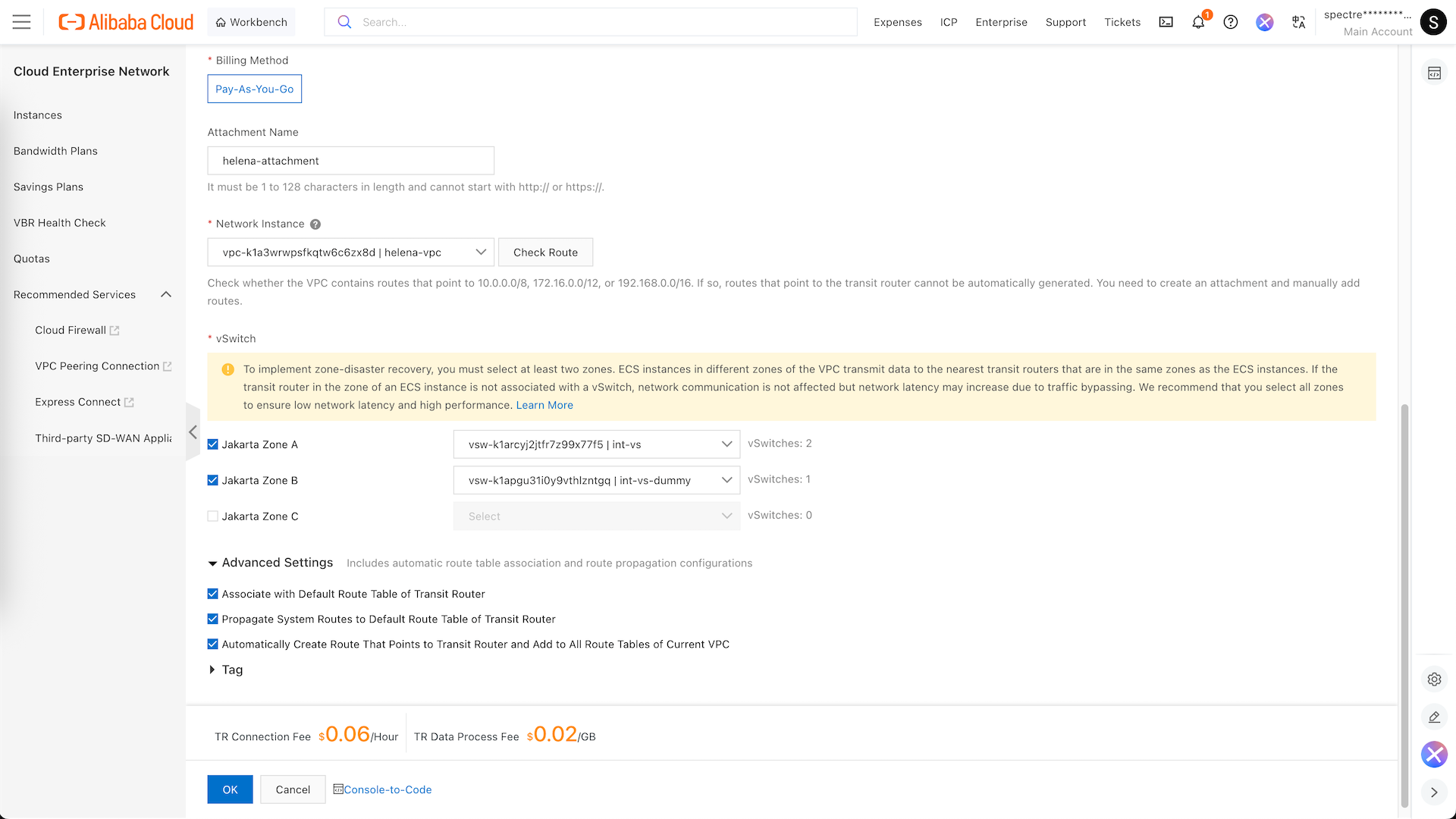
The first one is to our helena-vpc, here we select the int-vs along with its dummy
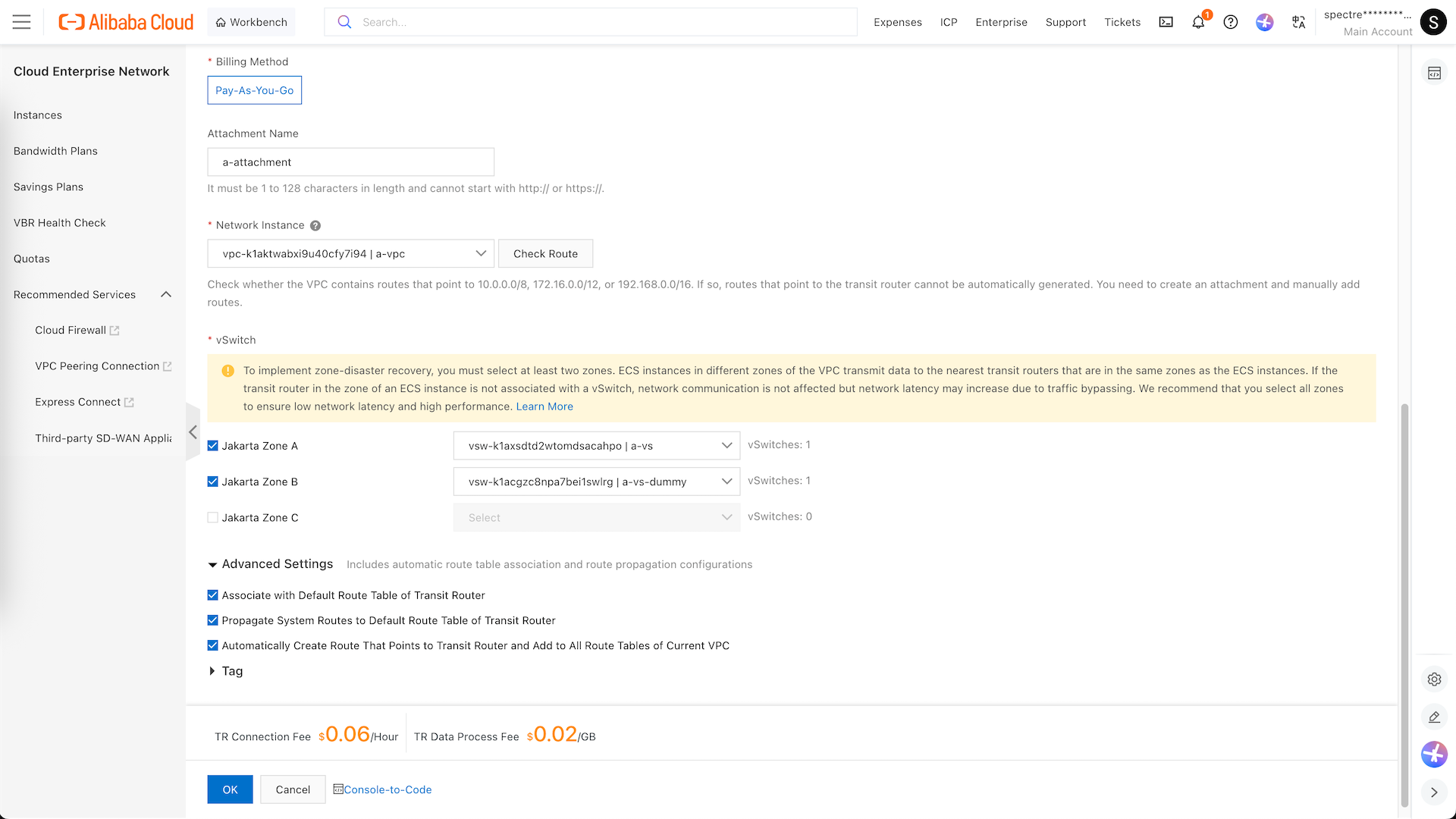
Then the a-vpc
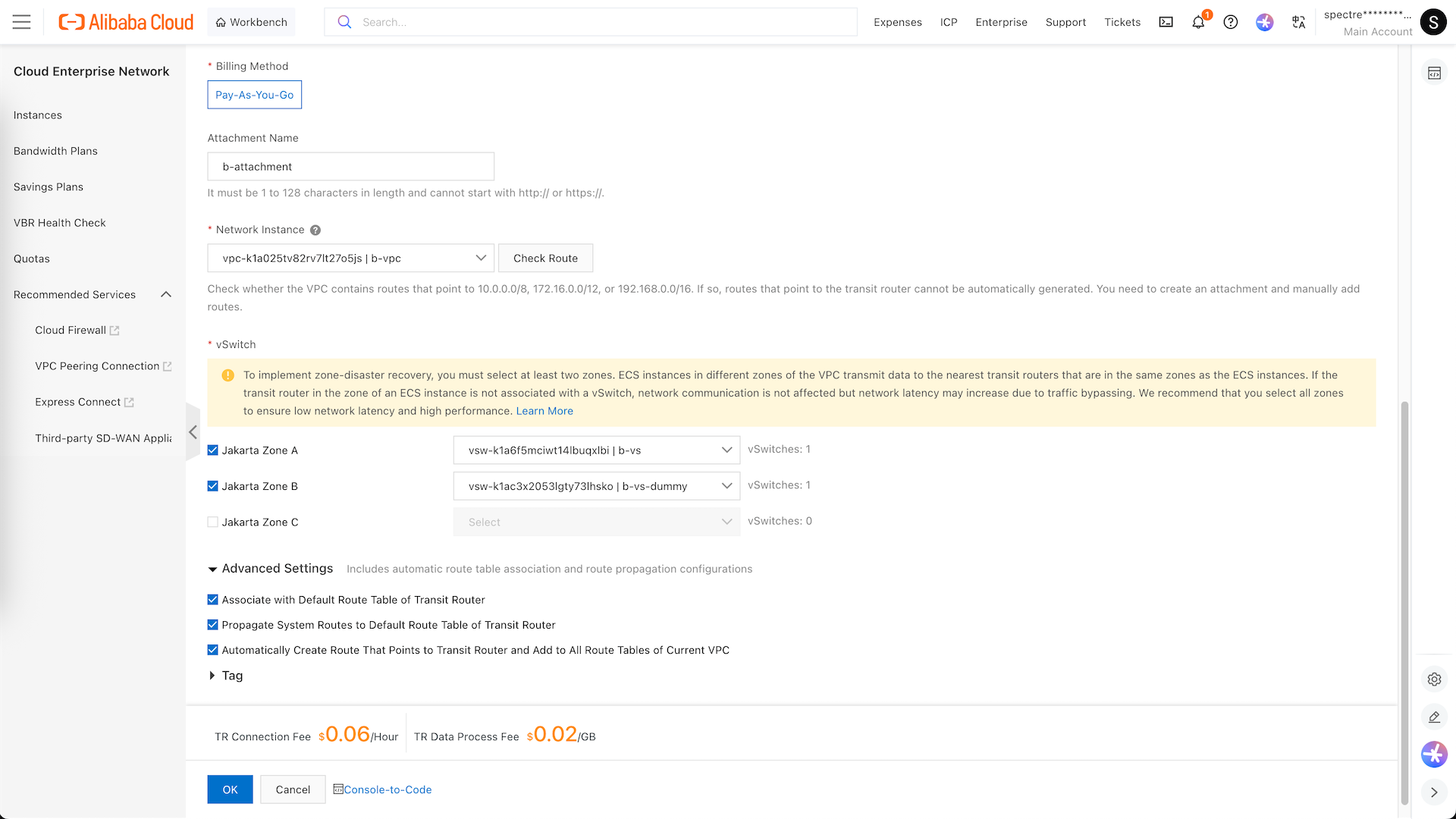
And the b-vpc
Now we have all connections to the 3 VPCs set up
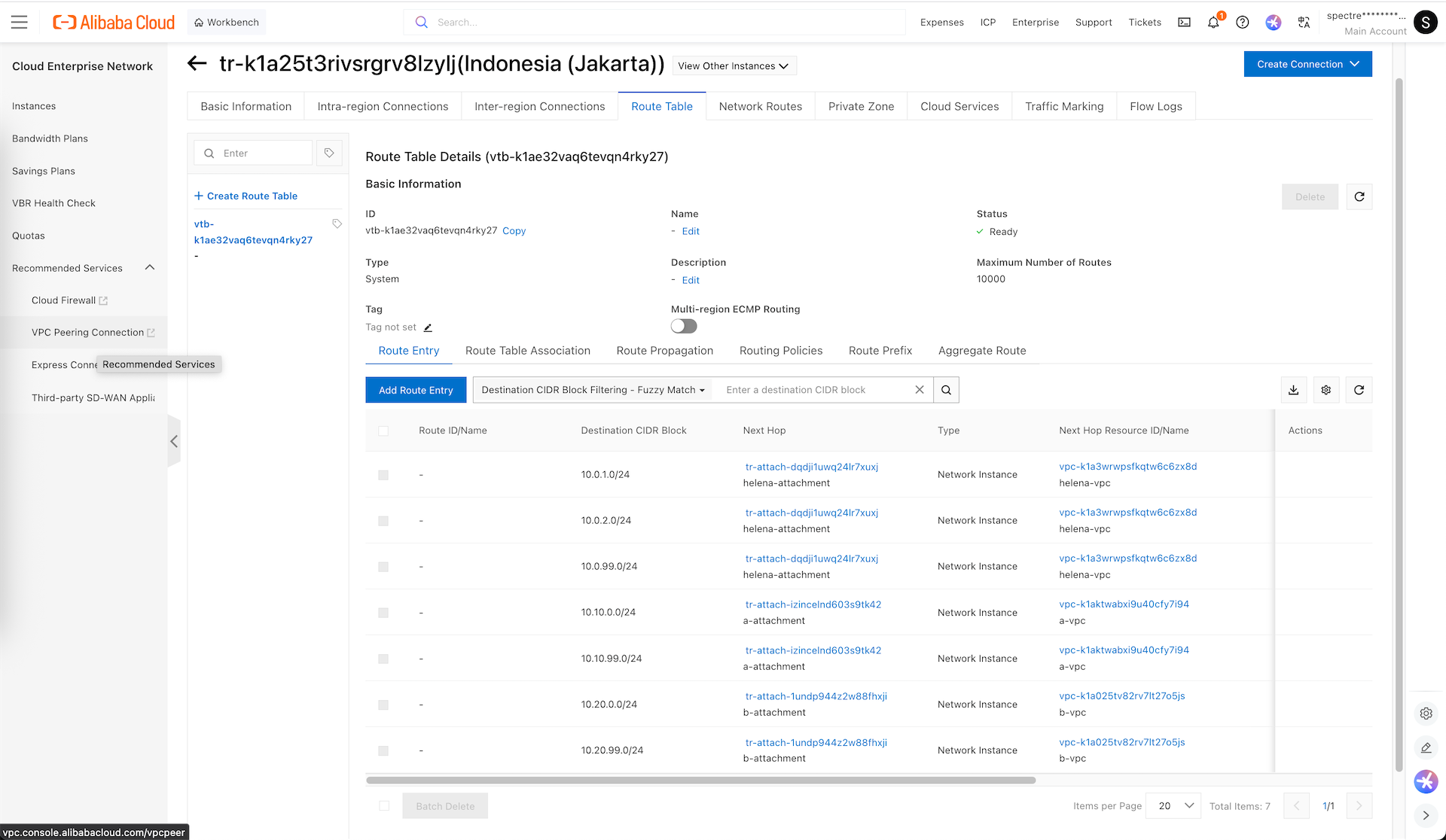
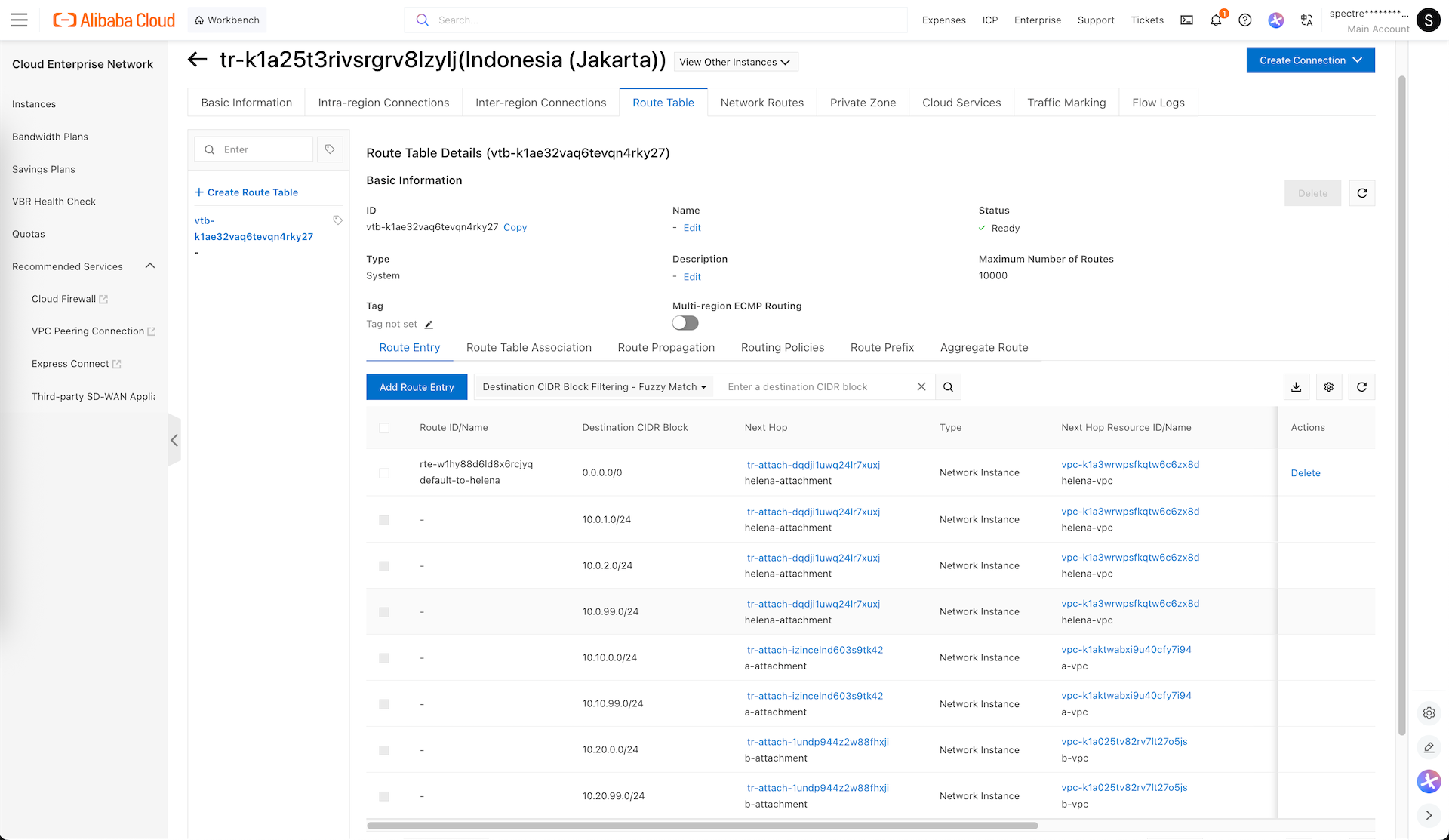
Next open the Transit Router’s Route Tables, here we can see all the routes going to each VPCs are already configured
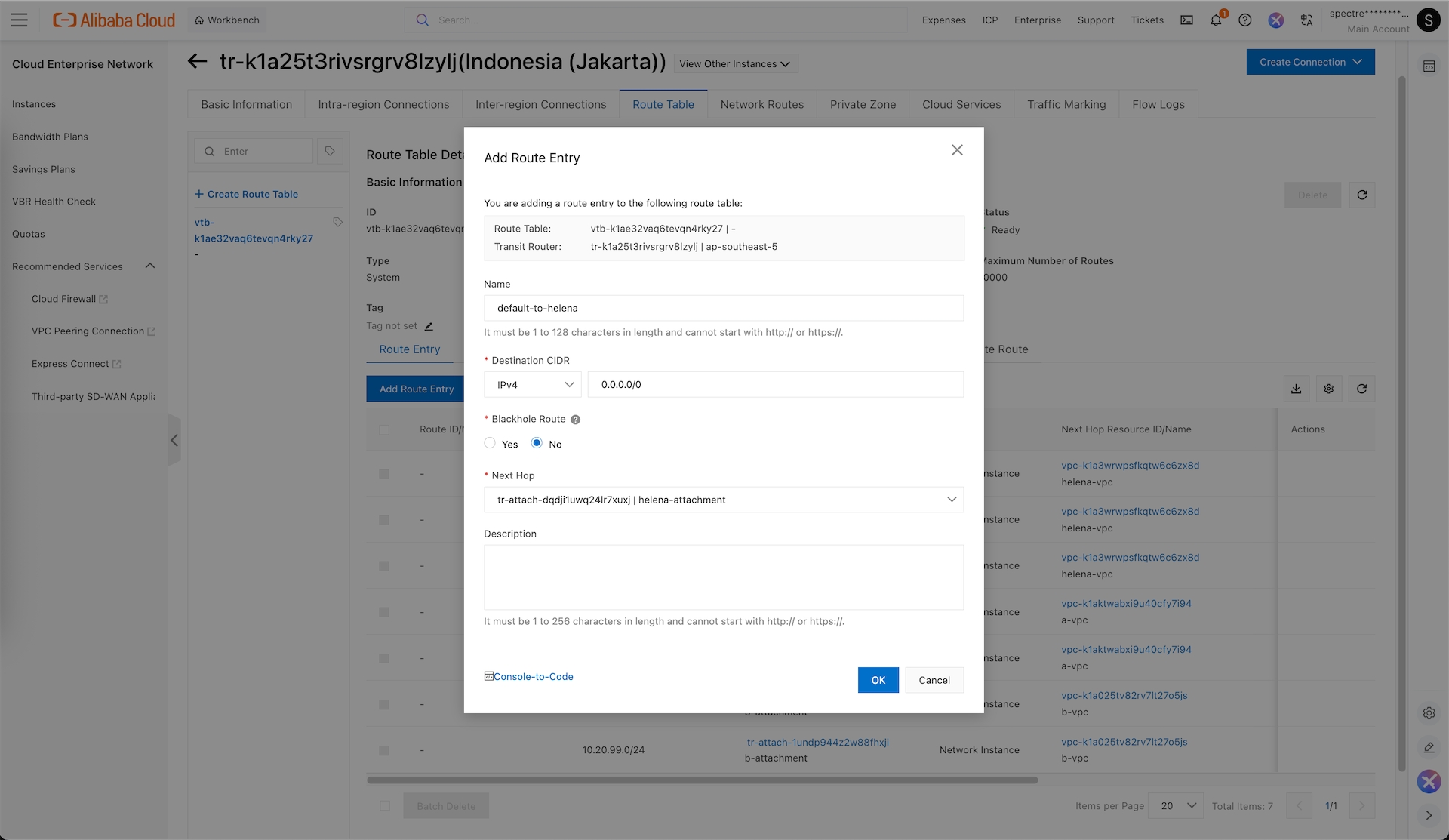
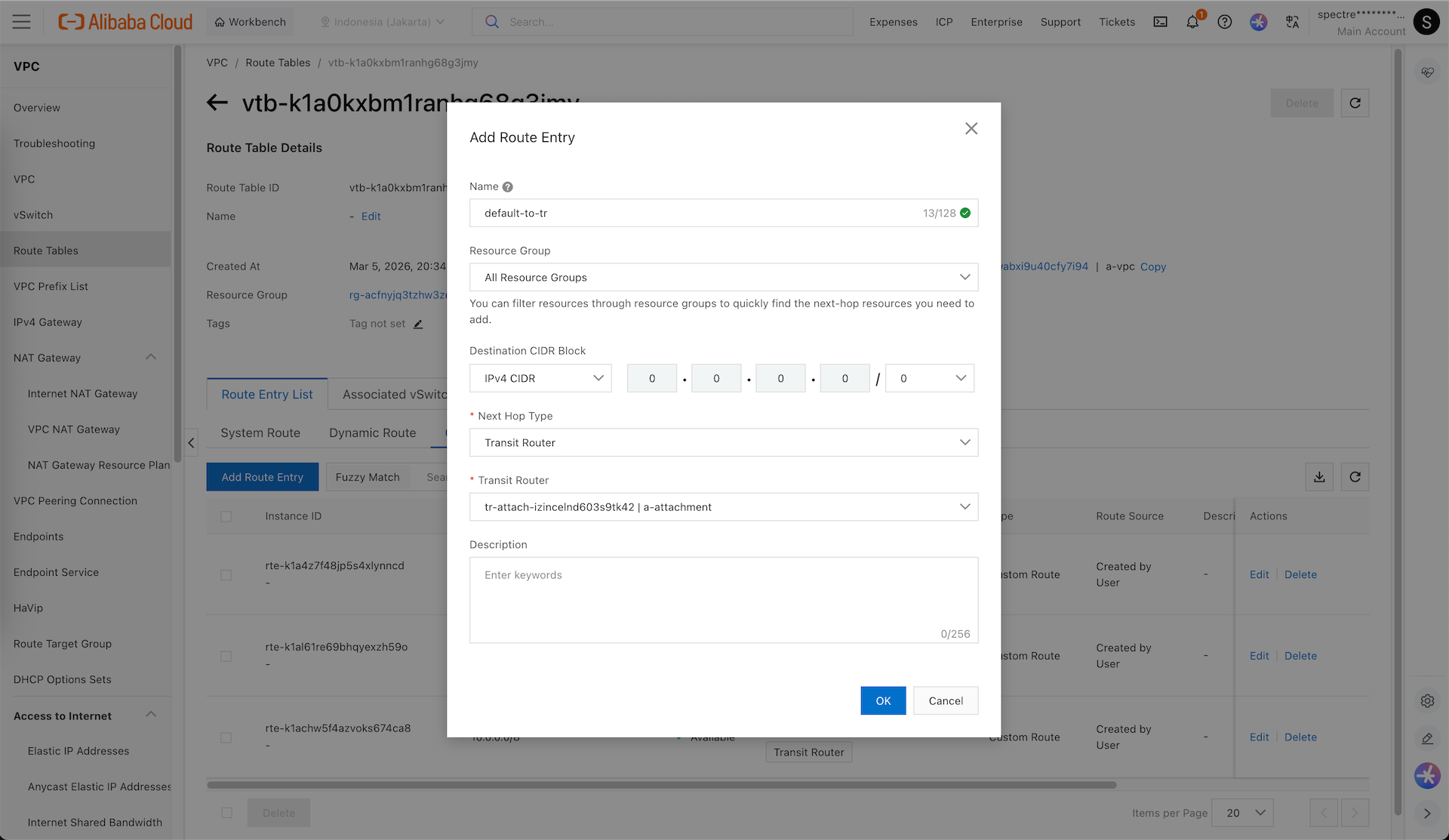
Add new route, this route will route all default traffic to our helena-vpc
VPC
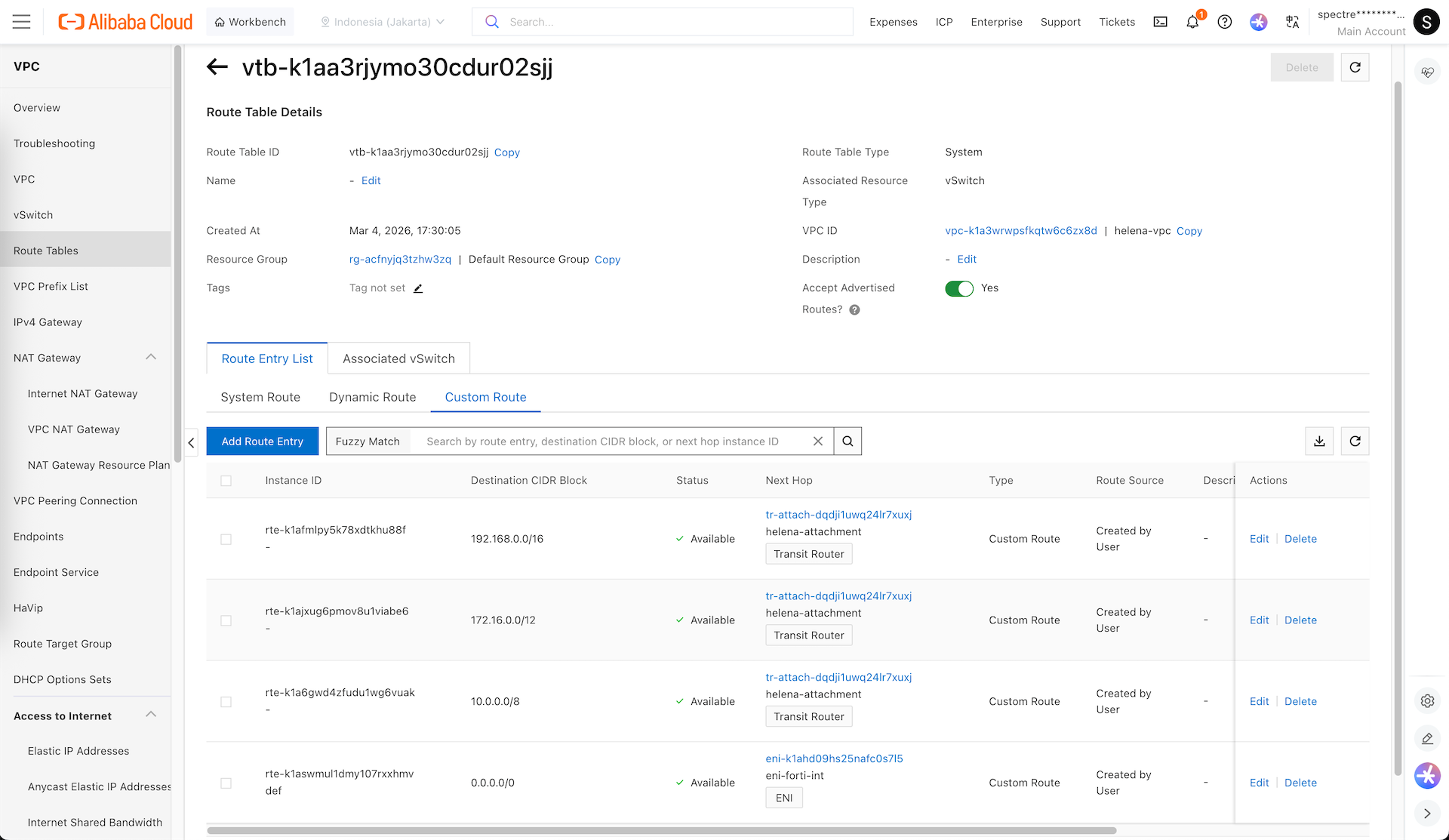
Now we go back to our VPCs configurations, we will add default routes on each vSwitch level so they all know to route traffic to our Transit Router
On a-vpc & b-vpc, we add a default route that sends traffic to our Transit Router
And on our helena-vpc’s int-vs, we add default route to send traffic to fortigate’s internal ENI
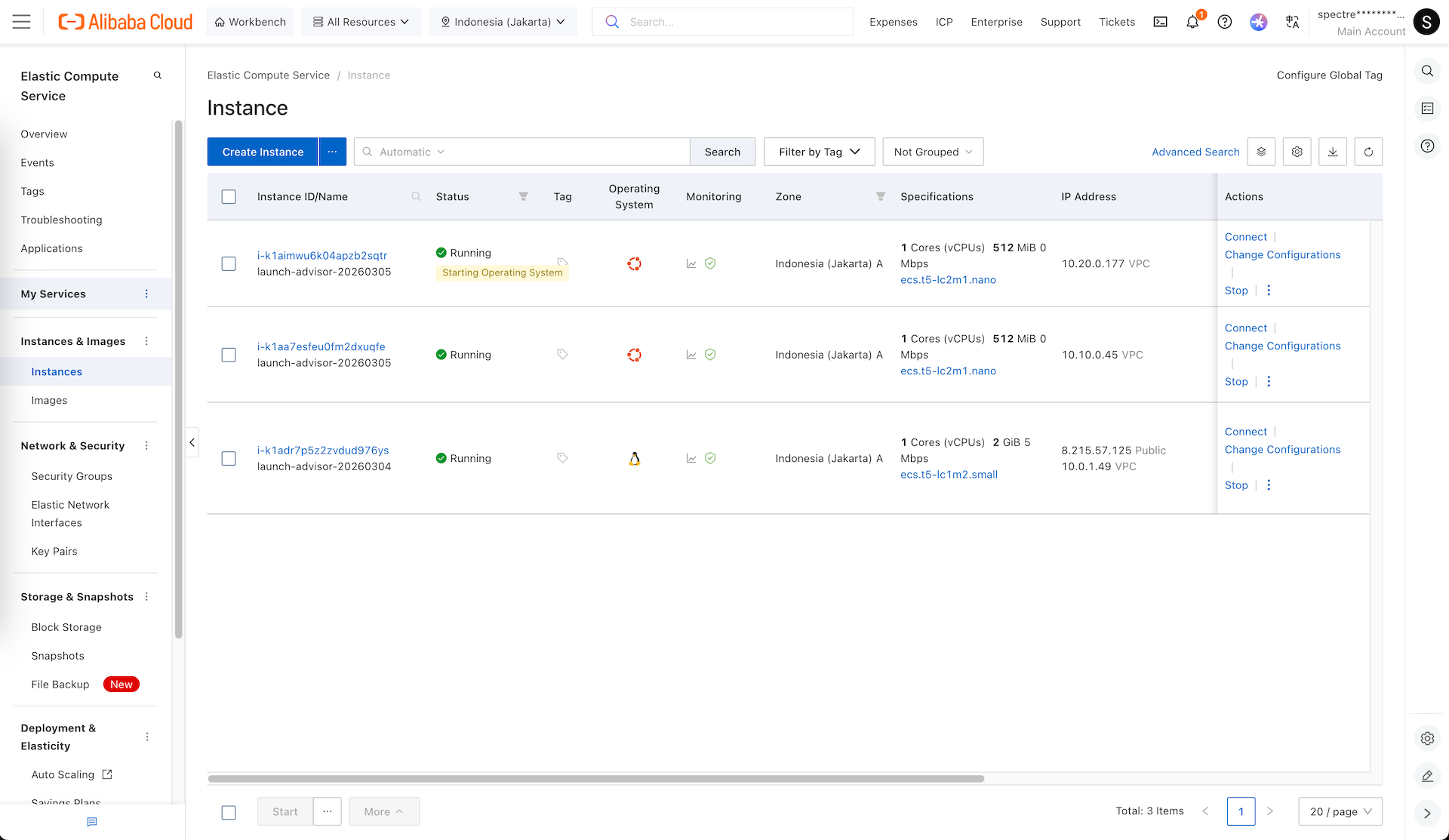
ECS
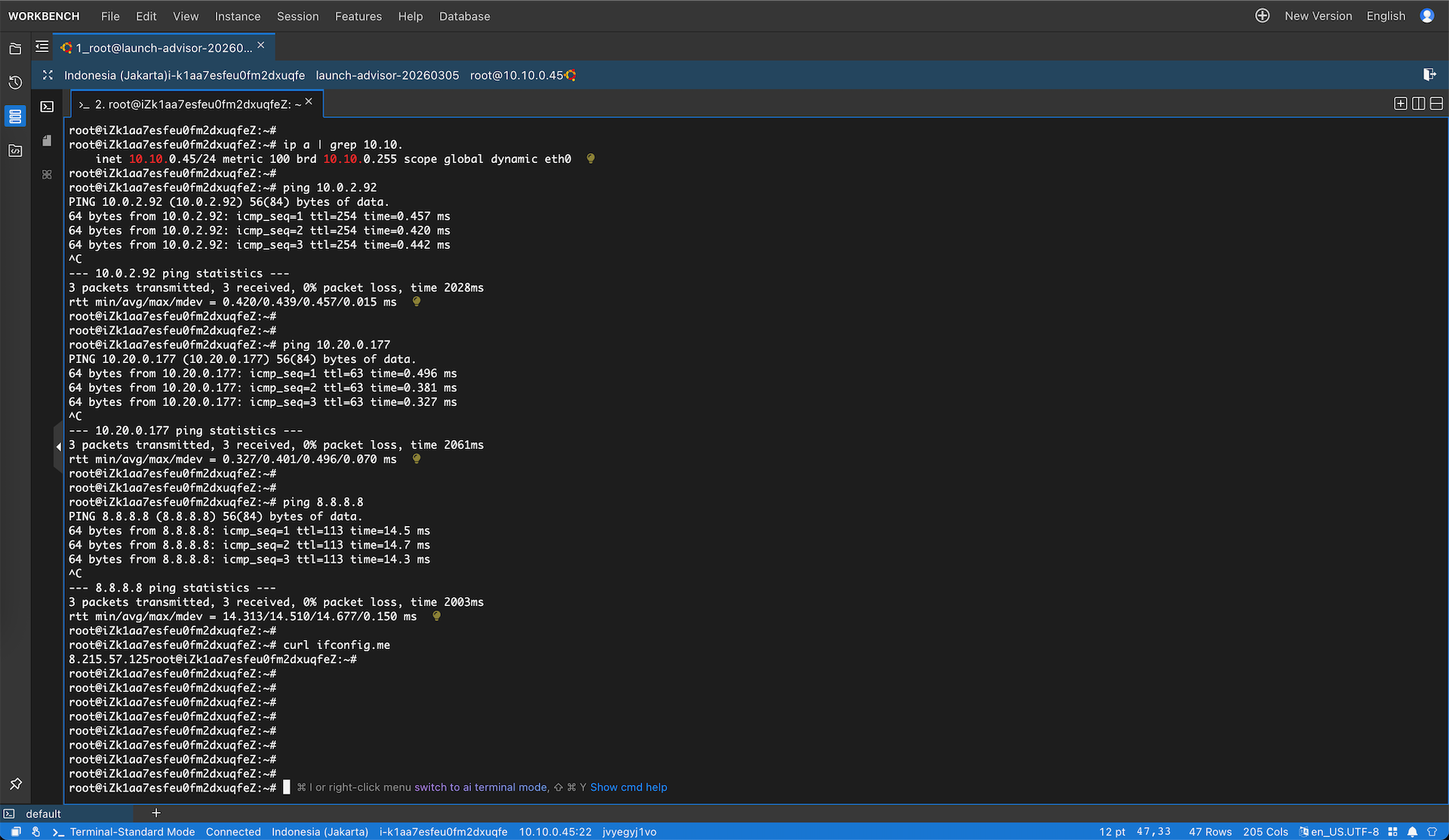
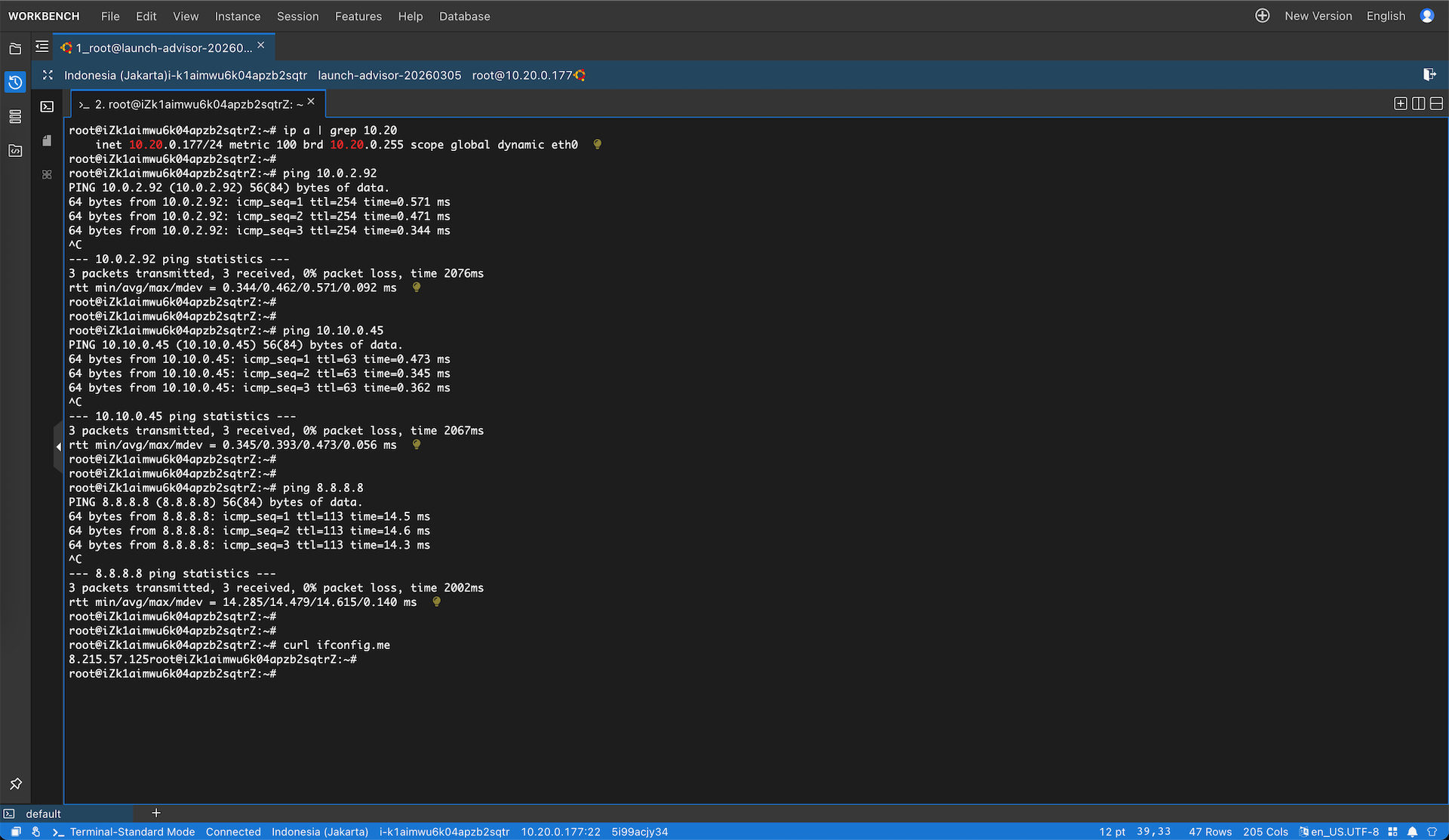
Next we spin up small linux vm on each a-vpc & b-vpc
On the client on a-vpc, we can see that we can connect to client on b-vpc and to internet
Same goes if the test is done from the client on the vpc-b side
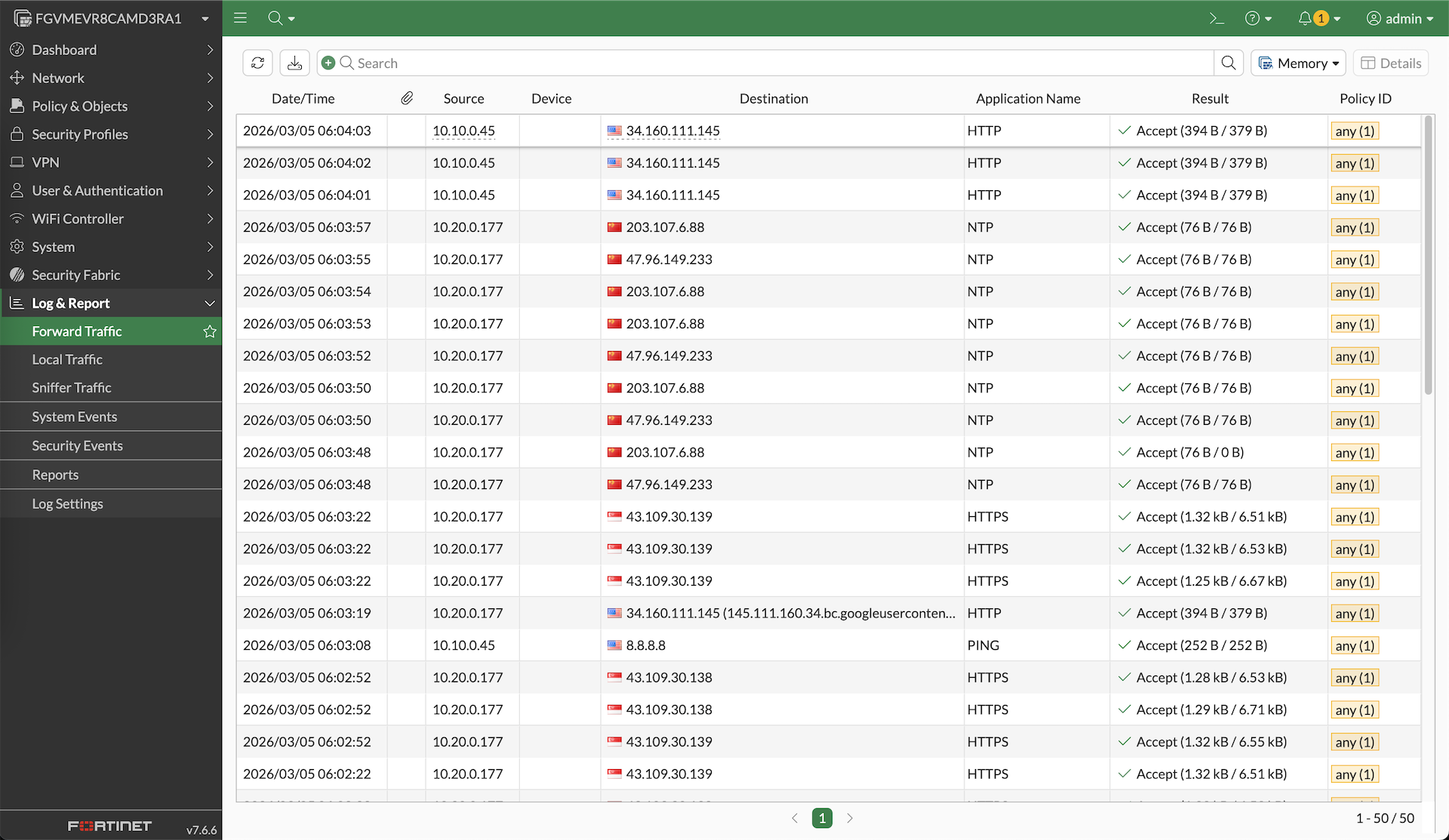
On fortigate, logs from both clients can be seen here, verifying that our CEN lab is working and all egress internet traffic is passed through our Fortigate firewall